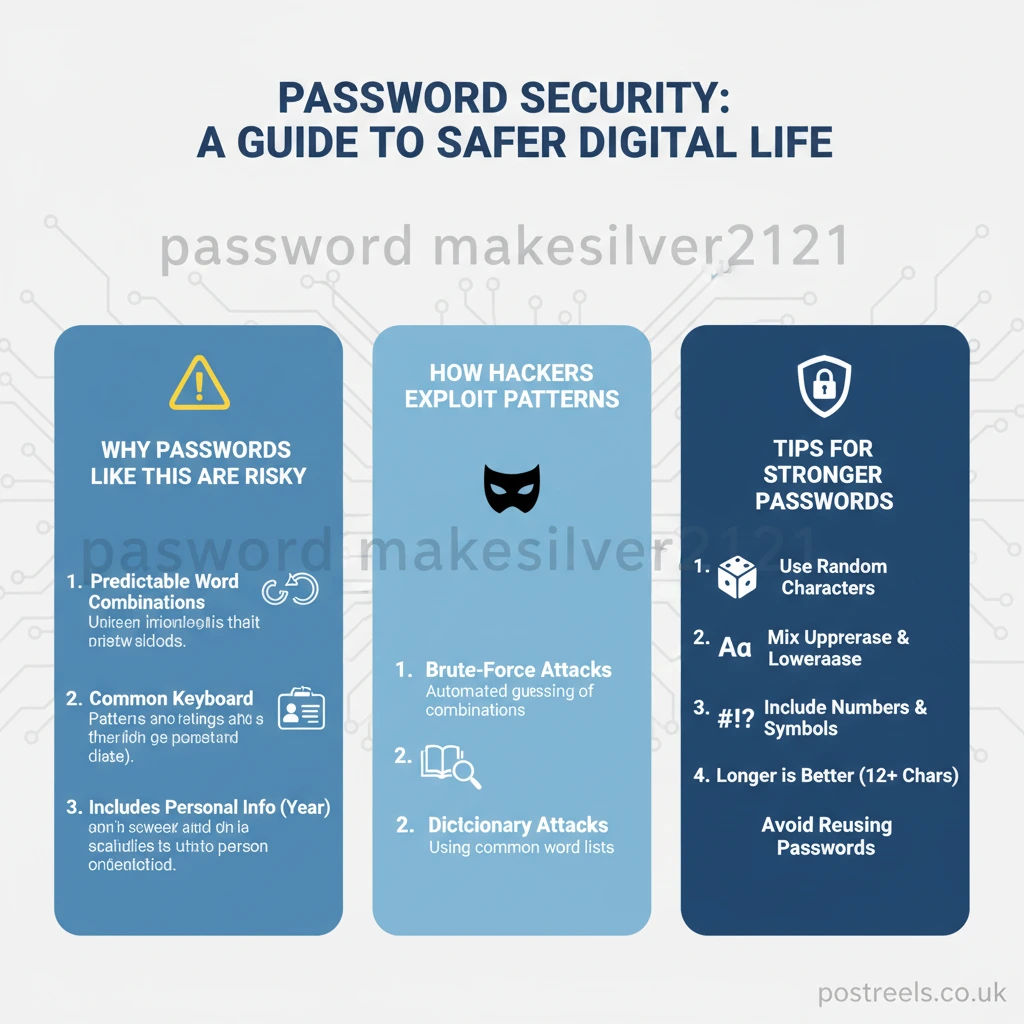
Have you ever wondered what makes a password strong or weak? You might see a string of text like password makesilver2121 and think it looks reasonably secure. It has words and numbers, and it’s a decent length. But this specific phrase is a perfect example of how our ideas about security can sometimes miss the mark. It highlights the common ways people create passwords and why those habits can put them at risk.
This guide will break down everything you need to know about the concept behind password makesilver2121. We will explore why it represents a common but flawed approach to online security. You will learn what makes a password truly safe, how hackers exploit predictable patterns, and what simple steps you can take to protect your digital life. This is not just a technical manual; it is a practical look at human behavior and how we can make smarter choices to keep our accounts secure.
What Does Password Makesilver2121 Actually Represent?
At its core, password makesilver2121 exemplifies a predictable password structure. It combines common dictionary words with a simple numeric pattern. Let’s break down its components to understand why it’s a security case study.
- Common Words: It uses the words “password,” “make,” and “silver.” These are all simple, recognizable words found in any dictionary.
- A Simple Pattern: The numbers “2121” form a repeating sequence. Humans are drawn to patterns because they are easy to remember.
Cybersecurity experts analyze phrases like this to understand user behavior. People want passwords that are easy to recall, so they lean on familiar words and numbers. While this feels like a good compromise between memorability and complexity, it creates a predictable formula. Attackers are well aware of these formulas and design their tools to test for them specifically.
Why Do People Create Passwords Like This?
The main reason is human psychology. Our brains are not designed to remember long, random strings of characters. We naturally gravitate toward things that have meaning. A phrase like password makesilver2121 feels logical. It is long enough to meet most website requirements, and it mixes letters with numbers. This creates an illusion of strength. The user feels they have created something complex, but in reality, they have followed a very common and guessable template. It is the digital equivalent of hiding your house key under the doormat—it feels clever, but it’s the first place a burglar would look.
How Do Hackers Exploit Common Password Patterns?
Hackers rarely sit and guess your password by hand. They use sophisticated, automated software that can try billions of combinations in seconds. These tools are designed to exploit the very habits that lead to passwords like password makesilver2121.
What is a Dictionary Attack?
A dictionary attack is a method where a program tries every word from a list, or “dictionary.” These lists contain millions of words from various languages, popular names, and common phrases. A hybrid attack takes this a step further. It combines dictionary words with common number sequences and symbols. For example, it would test “silver,” “silver123,” “silver2024,” and eventually, combinations like “makesilver2121.” Since this password is built from dictionary words, it is highly vulnerable to this type of attack.
What is a Brute-Force Attack?
A brute-force attack is simpler but can be just as effective. The software tries every possible combination of characters until it finds the correct one. While the length of password makesilver2121 makes it more resistant than a short password, its lack of true randomness is a weakness. The predictable structure allows attackers to narrow their search, making the process much faster. If they know people tend to add four-digit numbers at the end, they can focus their efforts there.
Is Password Length More Important Than Complexity?
There is a long-standing debate in cybersecurity about what matters more: a password’s length or its complexity (the mix of characters). The modern consensus is that length is often the most critical factor in creating a strong password. However, this comes with an important condition: the length must contribute to randomness.
A long password made of predictable elements, like passwordmakesilver2121, is not as strong as a shorter, truly random one. But a long and random password is the ultimate goal. Think of it this way: each character you add to a password increases the number of possible combinations exponentially. This makes it significantly harder for a brute-force attack to succeed.
For example, a security audit in a U.S. tech company found that employees using 15-character passphrases composed of random words were far less likely to be compromised than those using 8-character complex passwords. The longer passphrases, even without many symbols, took exponentially longer to crack.
| Password Example | Type | Estimated Crack Time |
|---|---|---|
password | Weak | Instantly |
P@ssw0rd1! | Common (Complex but Short) | Hours to Days |
password makesilver2121 | Predictable (Long but Not Random) | Days to Months |
BlueChairJumped!9Fish | Strong Passphrase (Long and Random) | Centuries or more |
Crack times are estimates and depend on the attacker’s computing power.
What Is a Passphrase and Why Is It Better?
A passphrase is one of the best ways to create a strong, memorable, and secure credential. Instead of a single word, you use a string of several unrelated words. For example, CorrectHorseBatteryStaple.
Here’s why passphrases work so well:
- They Are Long: Combining four or five random words easily creates a password that is 20-30 characters long. This length provides immense protection against brute-force attacks.
- They Are Memorable: While the words are random, our brains can easily remember a short, quirky sentence. BlueChairJumped!9Fish is much easier to recall than x7$zPq!4#vK&.
- They Are Random (When Done Right): The key is to choose unrelated words. Do not use a line from a famous book or song, as those are included in attacker dictionaries. The more random the words, the higher the security.
To make a passphrase even stronger, you can add a number or a symbol. But even without them, the length alone provides a massive security boost.
Should You Use a Password Manager?
For many people, trying to remember dozens of unique, long passphrases is not practical. This is where password managers come in. A password manager is an encrypted digital vault that stores all your login information securely.
How Does a Password Manager Improve Security?
A password manager solves the biggest weaknesses in human password habits.
- Generates Strong Passwords: It can create long, truly random passwords for every account. You no longer have to think of them yourself.
- Eliminates Reuse: Since you do not have to remember the passwords, you can have a unique, uncrackable password for every single website. This prevents credential stuffing attacks, where a breach on one site compromises your other accounts.
- Simplifies Your Life: You only need to remember one strong master password to unlock your vault. The manager then automatically fills in your credentials on websites and apps.
Many people worry about storing all their passwords in one place. However, reputable password managers use zero-knowledge encryption. This means only you can access your data; even the company that makes the software cannot see your passwords.
Why Is Multi-Factor Authentication Essential?
Even the strongest password can be stolen. A phishing attack, where you are tricked into entering your password on a fake website, can bypass your defenses. A data breach at a company you use could also expose your credentials. This is why multi-factor authentication (MFA), also known as two-factor authentication (2FA), is so important.
MFA adds a second layer of security to your accounts. After entering your password, you must provide a second piece of evidence to prove it’s really you. This could be:
- Something you have: A code from an authenticator app on your phone, an SMS text message, or a physical security key.
- Something you are: Your fingerprint or a face scan (biometrics).
With MFA enabled, even if a hacker steals your password makesilver2121, they still cannot get into your account. They would also need your phone or your fingerprint, making it much harder to gain unauthorized access.
What Are Some Real-Life Consequences of Weak Passwords?
The risks associated with weak passwords are not just theoretical. In 2021, a major U.S. oil pipeline was shut down by a ransomware attack. Investigations revealed that the hackers gained initial access using a single compromised password for a virtual private network (VPN) account. The account did not have multi-factor authentication enabled. This one weak link led to a national infrastructure crisis, causing gas shortages and panic buying across the East Coast.
On a personal level, the consequences can be devastating. A person using the same simple password for their email and social media could have their accounts taken over. The attacker could then use the email to reset passwords for banking and other sensitive accounts, leading to financial theft and identity fraud. These scenarios happen every day and often start with a password that felt “good enough.”
Key Takeaways for Better Password Security
Protecting your digital life does not have to be complicated. By moving past outdated habits represented by phrases like password makesilver2121, you can build a strong defense.
- Prioritize Length: Aim for passwords that are at least 16 characters long. Passphrases are an excellent way to achieve this.
- Embrace Randomness: Avoid using personal information, common words, or predictable patterns. Use a random mix of unrelated words.
- Never Reuse Passwords: Every account deserves a unique password. A password manager is the best tool for this.
- Enable Multi-Factor Authentication: Turn on MFA for every account that offers it. It is your most important safety net.
- Stay Vigilant: Be wary of phishing emails and suspicious links. No legitimate company will ask for your password via email.
Conclusion
The phrase password makesilver2121 is more than just a string of characters; it’s a lesson in digital security. It teaches us that our instincts for creating memorable passwords often lead us down a predictable and vulnerable path. True online safety comes from understanding how attackers think and using modern tools and strategies to counter them.
By shifting your focus from simple, patterned words to long, random passphrases, you dramatically increase your security. Combining this with a password manager and multi-factor authentication creates a layered defense that is difficult for even the most determined hackers to break. The next time you create a password, remember the lessons from password makesilver2121 and choose strength over simple convenience.
Frequently Asked Questions (FAQs)
Is password makesilver2121 a real password that was leaked?
It is generally used as a representative example of a common password structure. While similar passwords have certainly appeared in data breaches, this specific phrase is most often used for educational purposes to discuss security flaws.
What if I add a symbol to a password makesilver2121?
Adding a symbol, like makesilver2121!, makes it slightly stronger. However, it does not fix the underlying problem of using predictable dictionary words and number patterns. Hackers’ tools are programmed to test for these common substitutions. A random passphrase is a much safer alternative.
How can I check if my passwords have been exposed in a data breach?
You can use a reputable service like “Have I Been Pwned?” to check if your email address or passwords have appeared in known data breaches. Many password managers also have this feature built-in and will alert you if one of your stored passwords has been compromised.
Are password managers really safe to use?
Yes, when you choose a reputable provider. Top-tier password managers use strong, end-to-end encryption, meaning your data is scrambled before it ever leaves your device. Only your master password can unscramble it. This is far more secure than reusing passwords or storing them in a spreadsheet.
Is biometric login (fingerprint or face ID) a replacement for passwords?
Biometrics are a convenient and secure form of multi-factor authentication, but they are not a full replacement for passwords yet. They are best used as a second layer of security or as a way to unlock your password manager. The combination of a strong master password and biometrics offers excellent protection.